Microsoft just released new information on a widespread malicious email campaign by Nobelium, the same hackers behind the massive SolarWinds incident.
This active campaign has already targeted 3,000 email accounts across 150 organizations. Microsoft reports the emails are crafted to look like they are from the United States Agency for International Development (USAID), including some that read “special alert” and “Donald Trump has published new documents on election fraud.”
The links go to Nobelium infrastructure and deliver a malicious file which allows hackers “persistent access to compromised machines.” Microsoft published this sample email screenshot from the malicious campaign.
Example email below:
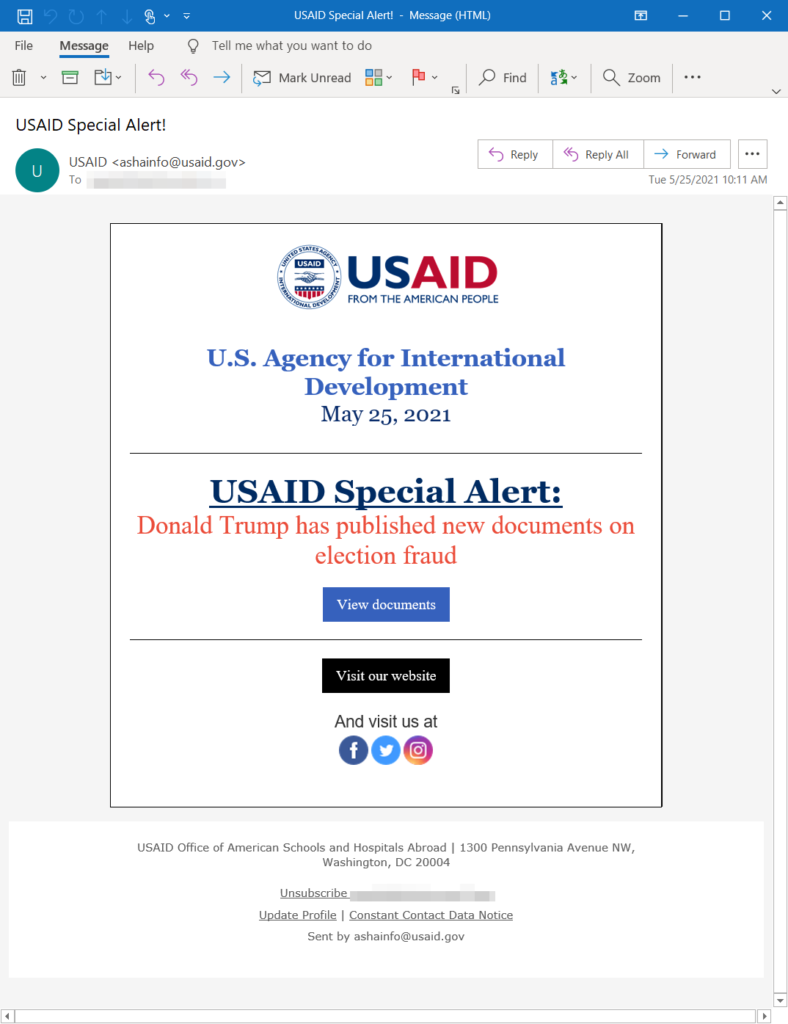
If you receive an email similar to this or purportedly from the USAID, please forward it to your IT department and do NOT click on any links in the email.
Node Prevent
When you purchase one of our cyber insurance policies you’ll receive vital cybersecurity updates such as this and online training courses to keep your employees up-to-date with the current cyber threats.
Attackers have developed two new business email compromise (BEC) phishing techniques that evade email security filters by manipulating Microsoft 365’s automated email responses.
- First the read receipts is manipulated.
- Then the target victims out-of-office (OOO) replies are redirected.
Both were seen being used in the United States in December 2020 during the holidays.
Step 1 – “Disposition-Notification-To” Read-Receipt Notification
With the read-receipts attack, the attacker creates an email and changes the “Disposition-Notification-To” email header to create a read-receipt notification from Microsoft 365 to the recipient.
The email should get caught by email security filters, but since it is created from the internal system, the read receipt is sent to the target, bypassing traditional security filters and is sent to the employee’s inbox,
Step 2 – Out-of-Office (OOO) Attack
With the OOO attack, a the attacker creates a BEC email impersonating someone inside the company. The attacker changes the “Reply-To” email header so that if the target has an OOO message turned on, that OOO notification (that includes the original text) is directed to someone else within the organisation.
Again, the message most likely will not be caught by email security filters, because it originates from the original target’s account, not externally.
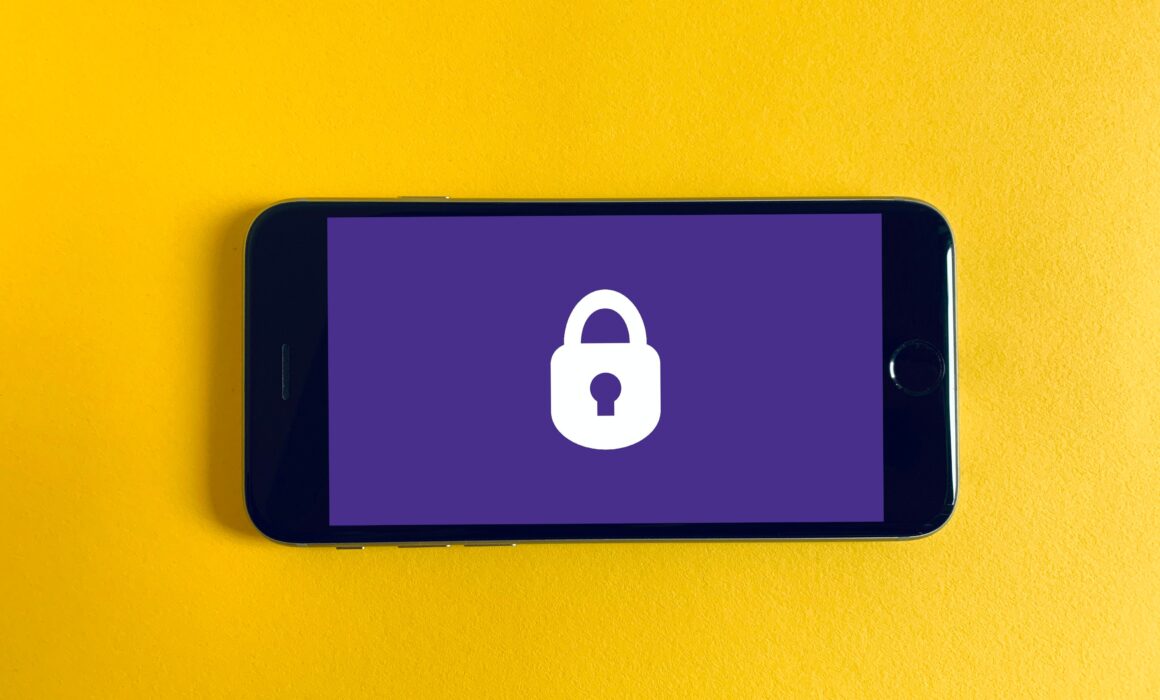
Business Email Compromise (BEC) is Still a Serious Email Threat
BEC emails are used to steal money from companies, often by impersonating an employee, vendor or customer in an email or mobile message. It often involves the attacker asking to pay a fake invoice, recurring payment or wire transfer.
The amount of BEC attacks continues to grow. According to Abnormal Security’s Quarterly BEC Report, BEC attacks rose by 15 percent quarter-over-quarter in Q3 of 2020.
BEC attacks rose by 15% quarter-over-quarter in Q3 of 2020.
Abnormal Security’s Quarterly BEC Report,
The average BEC attack volume per week during that time increased in six out of eight industries. The largest increase in BEC attacks was 93 percent in the energy/infrastructure sector. The highest number of weekly BEC attacks were in retail/consumer goods and manufacturing and technology. The study found these BEC campaigns used mostly invoice and payment fraud, with a 155 percent Quarter on Quarter.
The study found these BEC campaigns used mostly invoice and payment fraud, with a 155 percent Quarter on Quarter.
ABNORMAL SECURITY’S QUARTERLY BEC REPORT,
As email-security gets better, so do cybercriminals. For example, in early January a campaign was launched that leveraged Google’s Forms survey tool to create an ongoing conversation between the email recipient and the attacker which set up victims for future BEC attacks.
Microsoft and Office 365 are Big Targets
The Microsoft Office 365 cloud environment is a big target for BEC compromise as well.
Once hackers compromise an Office 365 environment, these BEC scammers can leverage trusted communications. For example, attackers can send an illegitimate email from the CEO’s official account to socially engineer employees, customers, or partners.
Attackers can also search through emails, chat histories and files to steal passwords or other important data. They can also set up forwarding rules to get access to emails without needing to sign in again. Furthermore, they could plant malware or malicious links into commonly used and trusted documents. The goal here is to manipulate something everyone trusts to bypass prevention controls that could trigger alerts to ultimately steal or hold files and data for ransom.
Protecting Against BEC Attacks
BEC attacks are hard to detect with typical tools and methods because they do not use malware or malicious URLs that can be detected by antivirus, so mitigating this threat can be difficult. Traditionally, the best defence for these kinds of attacks is end-user training and awareness so end-users can verify a request is indeed legitimate. It is also always a good idea to implement 2FA for email, configure your email to filter out suspicious looking phishing emails, and use updated end-point protection and antivirus.
An advanced Microsoft Office 365 phishing campaign is being launched at C-level executives, executive assistants, and financial departments.
Some of these attacks see newly-appointed, unannounced CEO’s as victims. In these cases, attackers try to take advantage of the executives during their transition period to gain unauthorized access to the account.
Attackers try to compromise any company account or a 3rd party partner and then use collected sensitive information to create more sophisticated attacks to phish C-level executives.
This campaign began in early December 2020 and is still ongoing as of March 2021. The attackers are leveraging phishing toolkits and many sophisticated methods.
Most of the phishing emails are sent from addresses with Microsoft-themed sender domains, with properly configured SPF records and are made to look like messages from the company, carrying fake alerts about “Important Service Changes”, “Important Security Policy Update”, etc.
The majority of the targeted email accounts used the format first name.last name@company domain, making full names in the attachments easy to automate. But even in cases where only initials appeared in the email address, the attackers still included the victim’s full name in the PDF attachment. This suggests the threat actors conducted additional prior research to carefully carry out spear phishing attacks.
Through malicious attachments, the victim is sent to a spoofed Microsoft-looking themed webpage with a fake Office 365 login page. If the victim enters their account credentials into the phishing portal, the attacker can then verify it was a valid Office 365 address. If after the victim enters their credentials, the victim may simply be redirected to the legitimate sign-in website like nothing ever happened.
How to Protect Yourself
Sophisticated phishing attacks are hard to detect with typical tools and methods because they do not use malware or malicious URLs that can be detected by antivirus. While it is important that you always use updated end-point protection and antivirus, mitigating this threat is hard. Here are some best practices:
- End-user training, awareness, and education is critical so end-users know to verify a request as legitimate and stay alert for unexpected emails with links or attachments. For example, employees should be on the alert for poor spelling and grammar and spoofed app names, domain URLs and email addresses.
- Implement two-factor authentication (2FA) for email. This is one of the best defences against phishing, because even if the attacker steals a user’s credentials, they won’t be able to gain access without the second factor.
- Configure your email to filter out suspicious looking phishing emails. Depending on your email filter, this may be turned on by default.
- Prohibit employees from being able to navigate to sites not whitelisted via a web filter. If you have a web filter, have your network administrator or authorized IT professional configure it to prohibit users from accessing unsafe and spoofed websites.
Node Prevent
When you purchase one of our cyber insurance policies we include Node Prevent, a free service with employee training, how to implement best practices and threat alerts such as these.
Phishing is when you receive an email that tricks you into clicking on a link to a fraudulent website and then sharing private information, or opening a malicious attachment on your phone, tablet or computer.
If you trust the link you could be giving away your user names, passwords, Social Security numbers, bank details or installing malware, like viruses, spyware or ransomware on your device and at work you could be handing over access to your company and all their sensitive data.
Phishing is the top cybercrime in the US. In 2019, the FBI reported that it had claimed nearly 115,000 victims with victim losses at $57.8 million, an average of $507 per victim.
Spotting the phishing attack
Don’t get complacent, the top branded security software (e.g. Norton, Bitdefender etc) are very good at taking out phishing emails before they hit your inbox. But, it’s a false sense of security as some still get through. In fact, in your personal life and as an employee, the next 100 emails you receive, possibly three or four will be phishing scam emails.
The most important golden rule. Change your mindset. Don’t trust emails and don’t click on a link in an email. I’m purposefully, stressing this as the golden rule, even though you think it to be too onerous and impractical. Nonetheless, for the next seven days examine every email (see tips below) and learn to change your mindset and start spotting phishing attempts. The extra time you spend on examining your inbox will build your confidence and you will feel much more confident about email management.
The only time you can trust an email is if it comes from an email address you recognise and the email doesn’t seem out of the ordinary. Even here, if it contains an attachment don’t click on it yet.
Make sure you double check the email address and not just the name. Give the sender a call if you are unsure. Malware is commonly passed between compromised emails accounts so even if the email address is correct that doesn’t mean someone else isn’t sending fraudulent emails from their account.
How to check for the signs of phishing. There are five signs:
- Poor grammar. As far as the US is concerned, most cyber criminals are based in overseas countries such as Russia, North Korea, Eastern Europe, China and Iran. For the majority, US English is a foreign language. They make spelling errors (although they have improved significantly in recent years) and make grammatical errors (much harder to improve upon). In fact, as you read the email you will make an on-the-spot judgement – this is well written, this is poorly written. If it is poorly written be wary.
- Suspicious logo. If the email is topped with the logo of a known trusted business or government department, then check it against the official website with a quick Google. False logos can have washed out colours, faded edges or imprecise proportions. In effect, it could be a poor copy and paste job.
- Check the URL. Imagine you receive an email from NETFLIX containing a link. If you hover over the link (DON’T CLICK!) a small display will appear containing www.netflix.com plus suffices. You’ve validated the email that it is from NETFLIX. Job done. Imagine it reported www.netfilx.com or www.netflics.com then DO NOT click on the link. It’s false and belongs to a cybercriminal. In fact, any errors, whether spelling or design is a warning. Be super-cautious.
- Check the greeting. On my domestic accounts very rarely do I receive the greetings, ‘Dear customer’, ‘Dear subscriber’, ‘Dear friend’ or the more informal,’ Hi customer’, ‘Hi subscriber’. They say, ‘Dear Neil’ or ‘Hi Neil’. This is how customer-orientated domestic businesses tend to interact with their customers. Foreign cybercriminals make mistake ‘out-of-culture’ errors on greetings and/or sign offs.
- Attachments. Legitimate companies don’t send attachments that you didn’t ask for and also would not request sensitive information via email.
If all are followed with the instruction to click on the link to learn more and/or correct the problem. Be super-cautious.
About Node International
We provide leading comprehensive insurance coverage combined with essential cybersecurity prevention and detection tools.
Important Recommendation
Menu
Legal
Our Office :
One Minster Court
Mincing Lane
London
EC3R 7AA
Interested in Cyber Insurance?
[mc4wp_form id=”5523″]


Recent Comments