The General Data Protection Regulation (GDPR) is a broad-sweeping EU privacy law designed to increase an individual’s right to control personal data. Learn about GDPR, whether it applies to you, and how to get started with compliance issues. The GDPR materials presented here are informational only. For specific questions about GDPR compliance, please consult a trained professional.
WHAT IS GDPR?
The General Data Protection Regulation (GDPR) is a European Parliament regulation that came into effect on May 25, 2018. The regulation is designed to harmonise data privacy laws across Europe with the intention to protect and strengthen the privacy rights of EU residents.
COMMON GDPR TERMS
Data controller means the person(s) who determine the purposes and means of processing personal data.
Data exporter means a controller (or, where permitted, a processor) established in the EU that transfers personal data to a data importer.
Data importer means a controller or processor located in a third country that receives personal data from the data exporter.
Data processor means a person or entity that processes personal data on behalf of a controller.
Data subject means an individual who is the subject of the relevant personal data.
Personal data means any information related to a natural person or ‘Data Subject’, that can be used to directly or indirectly identify the person. It can be anything from a name, a photo, an email address, bank details, posts on social networking websites, medical information, or a computer IP address.
Processing means any operation that is performed on personal data.
Sensitive Data means personal data that reveals racial or ethnic origin, political opinions, religious or philosophical beliefs, trade-union membership, and data concerning health or sex life. Sensitive data are subject to additional protections.
WHAT INFORMATION DOES THE GDPR APPLY TO?
The GDPR applies to personal data and sensitive personal data.
GDPR PRINCIPLES
The GDPR is based on the following privacy and data collection principles and requires that personal data be:
(a) processed lawfully, fairly and in a transparent manner to individuals
from which it is collected;
(b) collected for specified, explicit and legitimate purposes and not further
processed contrary to any of those purposes;
(c) adequate, relevant and limited to what is necessary in relation to the
purposes for which it is processed;
(d) accurate and, where necessary, kept up to date;
(e) kept in a form which permits identification of data subjects for no longer than is necessary for the purposes for which the personal data are processed; and
(f) processed in a manner that ensures appropriate security of the personal data.
IMPORTANT NOTE:
The data controller is responsible for, and must be able to demonstrate, compliance with the Data Protection Principles.
Help educate your employees on fraud this International Fraud Awareness week.
Learn what fraud is, why it’s important to stop it, red flags to look for and ways to prevent it with the guide by ACFE.
Find more resources here: https://www.fraudweek.com/

The U.S. government is working with the private sector to bolster the country’s cybersecurity, the White House recently announced. During a meeting on Aug. 25, President Joe Biden called on companies to “raise the bar on cybersecurity” and outlined a number of initiatives to address the growing threat of cybercrime, including plans for the National Institute of Standards and Technology to work with industry partners on new cybersecurity guidelines.
The news came just months after a May ransomware attack temporarily shut down the Colonial Pipeline, one of the largest fuel pipelines in the U.S., causing gas shortages and consumer panic-buying. This and other recent cyberattacks threatening American infrastructure make cybersecurity a fitting national priority, said Matthew Lefchik, Director, Cyber Risk Management, Node International, Detroit/Farmington Hills, Michigan.
“The Colonial Pipeline attack was so significant because it really disrupted consumers,” he said. “The government is seeing these recent attacks impacting the supply chain and getting involved not only because of the impact on consumers, but also there is relevance to who these bad actors are, and we do not want to be paying them.”
Insurance carriers have also joined the Biden administration’s plans to combat cybercrime, with one provider saying policyholders will need to meet certain cybersecurity standards to access Cyber & Privacy Liability Insurance coverage, and another committing to make cyber risk assessments and monitoring free for any organization, the White House noted in its announcement.
The government is seeing these recent attacks impacting the supply chain and getting involved not only because of the impact on consumers, but also there is relevance to who these bad actors are, and we do not want to be paying them.
Matthew Lefchik
Find the full article here.
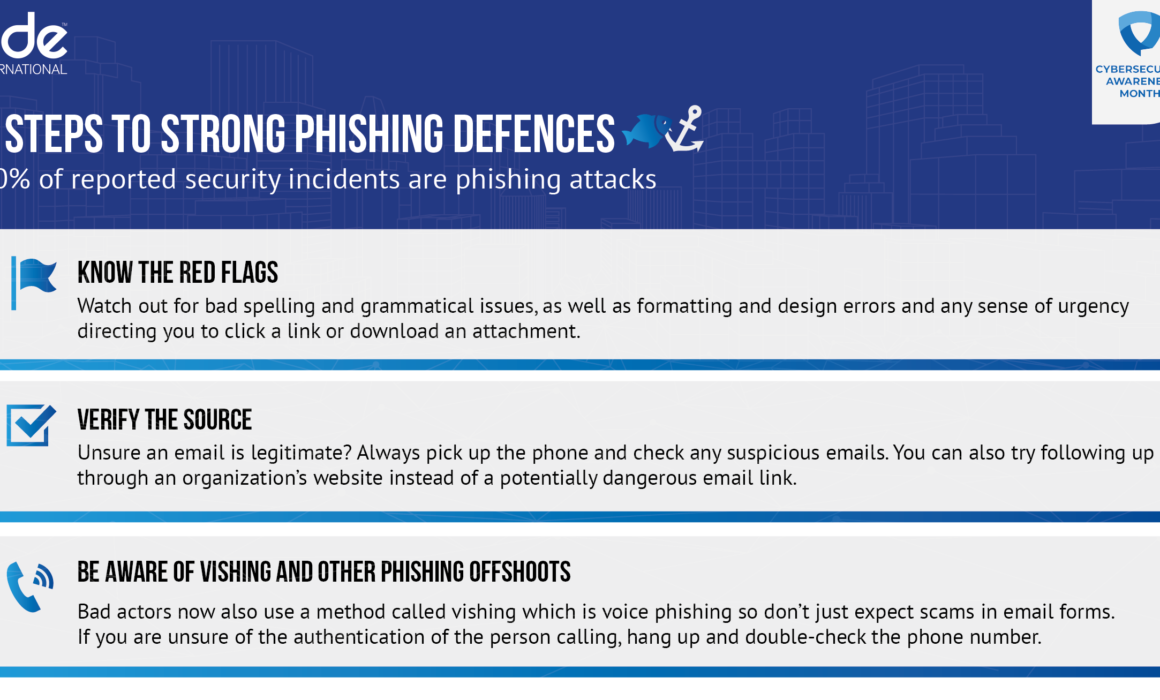
From ransomware to SolarWinds, the cybersecurity space has been as hectic as it has ever been over the last 12-24 months. However, for all of the emerging threats and news that are cropping up on the horizon, phishing — one of the oldest pain points in cybersecurity — is continuing to quietly wreak havoc, and is as big of a threat as it has ever been.
Despite often being overlooked in terms of hype, phishing has been a mainstay in the cybersecurity threat landscape for decades. In fact, 43 percent of cyberattacks in 2020 featured phishing or pre-texting, while 74 percent of US organizations experienced a successful phishing attack last year alone. That means that phishing is one of the most dangerous “action varieties” to an organization’s cybersecurity health. As a result, the need for proper anti-phishing hygiene and best practices is an absolute must.
With that in mind, here are a few quick best practices and tips for dealing with phishing threats.
- Know the Red Flags
Phishes are masters of making their content and interactions appealing. From content design to language, it can be difficult to discern whether content is genuine or a potential threat, which is why it is so important to know the red flags. Awkward and unusual formatting, overly explicit call outs to click a hyperlink or open an attachment, and subject lines that create a sense of urgency are all hallmarks that the content you received could be potentially from phish and indicate that it should be handled with caution.
2. Verify the Source
Phishing content comes in a variety of ways, however, many phishes will try to impersonate someone you may already know — such as a colleague, service provider or friend — as a way to trick you into believing their malicious content is actually trustworthy. Don’t fall for it. If you sense any red flags that something may be out of place or unusual, reach out directly to the individual to confirm whether the content is authentic and safe. If not, break-off communication immediately and flag the incident through the proper channels.
3. Be Aware of Vishing and Other Phishing Offshoots
As more digital natives have come online and greater awareness has been spread about phishing, bad actors have begun to diversify their phishing efforts beyond traditional email. For example, voice phishing — or vishing — has become a primary alternative for bad actors looking to gain sensitive information from unsuspecting individuals. Similar to conventional phishing, vishing is typically executed by individuals posing as a legitimate organization — such as a healthcare provider or insurer — and asking for sensitive information. Simply put, it is imperative that individuals be wary of any sort of communication that asks for personal information whether it be via email, phone or chat — especially if the communication is unexpected. If anything seems suspicious, again, break-off the interaction immediately and contact the company directly to confirm the veracity of the communications.
—
Phishing may be “one of the oldest tricks in the book,” but it is still incredibly effective. And although it may be hard to spot when you may be in the midst of a phishing attempt, by exercising caution and deploying these few fundamentals, individuals and organizations more broadly can drastically mitigate the chances of falling victim to a phishing attack.
Learn the Cyber Basics this Cybersecurity Awareness Month
At a time when we are more connected than ever, being “cyber smart” is vital. This year has already seen more than a fair share of attacks and breaches, including the SolarWinds and Kaseya breaches as well as high-profile attacks on the Colonial Pipeline and other critical infrastructure.
Cyber attacks are becoming more sophisticated with more evolved bad actors cropping up each day. Luckily, there are several steps that we can take on a daily basis to mitigate risks and stay one step ahead of malefactors. Here are a few quick tips:
- Enable MFA
Multi-factor authentication (MFA) adds that necessary second check to verify your identity when logging in to one of your accounts. By requiring multiple methods of authentication, your account is further protected from being compromised, even if a bad actor hijacks your password. In this way, MFAs make it more difficult for password cracking tools to enable attackers to break into accounts.
- Use strong passphrases/password manager
This may seem obvious, but all too often securing strong passphrases/password managers is overlooked. People spending more time online during the pandemic has certainly contributed to more bad actors prowling for accounts to attack. Using long, complex, and unique passwords is a good way to stop your account from being hacked, and an easy way of keeping track and remembering your passwords is by using a password manager.
- Perform software updates
When a device prompts that it’s time to update the software, it may be tempting to simply click postpone, and ignore the message. However, having the latest security software, web browser, and operating system on devices is one of the best defenses against online threats. So, don’t wait – update.
- Do your research
Common sense is a crucial part of maintaining good online hygiene, and an intuitive step to stay safe online is to do some research before downloading anything new you are downloading to your device, such as apps. Before downloading any new learning app on your device, make sure that it’s a by checking who created the app, what the user reviews say, and if there are any articles published online about the app’s privacy and security features.
- Check your settings
Be diligent to double check your privacy and security settings, and be aware who can access your documents. This extends from Google docs, to Zoom calls, and beyond. For meetings on Zoom, for example, create passwords so only those invited to the session can attend, and restrict who can share their screen or files with the rest of the attendees.
—
Being cyber smart and maintaining stellar online hygiene is the best way to protect yourself and others from cyber attacks. No single tip is foolproof, but taken together they can make a real difference for taking control of your online presence. Following these tips is also easy, and free. By taking preventive measures and making a habit of practicing online safety, you can decrease your odds of being hacked exponentially – and prevent lost time and money, as well as annoyance.
Find out more about Cybersecurity Awareness Month here.
In 2020, the year of remote working, cyber crime increased by 80%. That’s equal to an attack every 39 seconds.
To help you avoid getting caught out, expert Karl Susman, Susman Insurance Agency, Cyberman365 reseller, reveals his top 5 tips on how to work remotely safely in the Spring edition of Tort, Trial & Insurance Practice Law Journal from the American Bar Association.
These are essential and easy to implement tips that anyone working from home can do, such as making sure your computer automatically updates.
Check out the featured spread here:
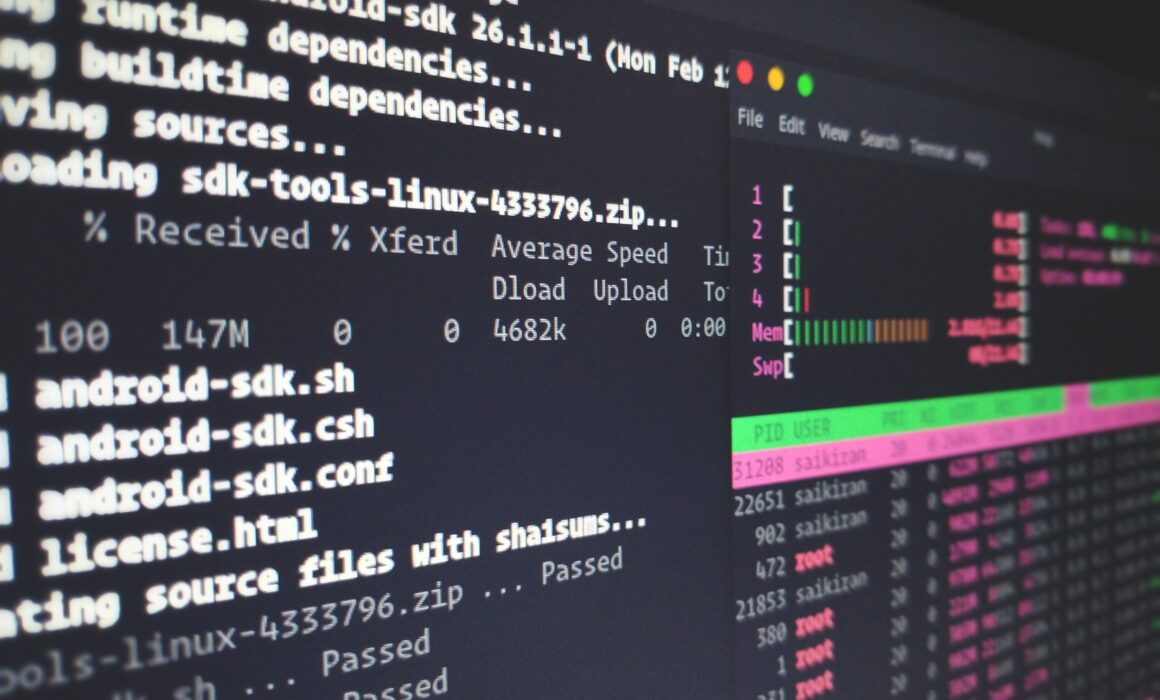
New backdoor malware targeting Linux operating systems has been discovered, hiding as a polkit daemon. It is has been named RedXOR for its network data encoding scheme based on XOR.
Analysing the Tactics, Techniques, and Procedures (TTPs), RedXOR is thought to be developed by Chinese threat actors. The malware samples have low detection rates in VirusTotal, and is used in targeting attacks against legacy Linux systems.
There are also many similarities between RedXOR and the reported malware associated with Winnti umbrella threat group known as the PWNLNX backdoor, as well as to XOR.DDOS and Groundhog, two botnets attributed to Winnti by BlackBerry. The below samples can be used for reference:
The samples are both unstripped 64-bit ELF files called po1kitd-update-k. Similarities between the samples includes the use of old open-source kernel rootkits, both use the CheckLKM function, and both provide the attacker with a pseudo-terminal using Python pty shells and many other similarities.
The malware makes a remote connection to the command and control server over a TCP socket. The traffic is made to look like HTTP traffic. The command and control server instructs the malware to execute different commands returned in the JSESSIONID cookie. The malware can also be updated by the attacker by sending commands to the malware. The malware can also create new remote shells to get a pseudo-terminal (pty) interface and can perform network tunnelling.
How to Detect and Respond
Use the information below to detect and respond this threat. We suggest using the following indicators of compromise to ensure the RedXOR and the files it creates do not exist in your environment:
Indicators of Compromise
RedXOR Hashes
0a76c55fa88d4c134012a5136c09fb938b4be88a382f88bf2804043253b0559f
0423258b94e8a9af58ad63ea493818618de2d8c60cf75ec7980edcaa34dcc919
Network
update[.]cloudjscdn[.]com
158[.]247[.]208[.]230
34[.]92[.]228[].216
Process name
po1kitd-update-k
File and directories created on disk
.po1kitd-update-k
.po1kitd.thumb
.po1kitd-2a4D53
.po1kitd-k3i86dfv
.po1kitd-nrkSh7d6
.po1kitd-2sAq14
.2sAq14
.2a4D53
po1kitd.ko
po1kitd-update.desktop
S99po1kitd-update.sh
Follow these steps if you are a victim of this malware:
- Kill the process.
- Delete all files related to the malware.
- Make sure your machine is clean and running only trusted code.
- Contact the Experts for assistance if needed.
Node Prevent
When you purchase one of our cyber insurance policies you’ll receive vital cybersecurity updates such as this and online training courses to keep your employees up-to-date with the current cyber threats.
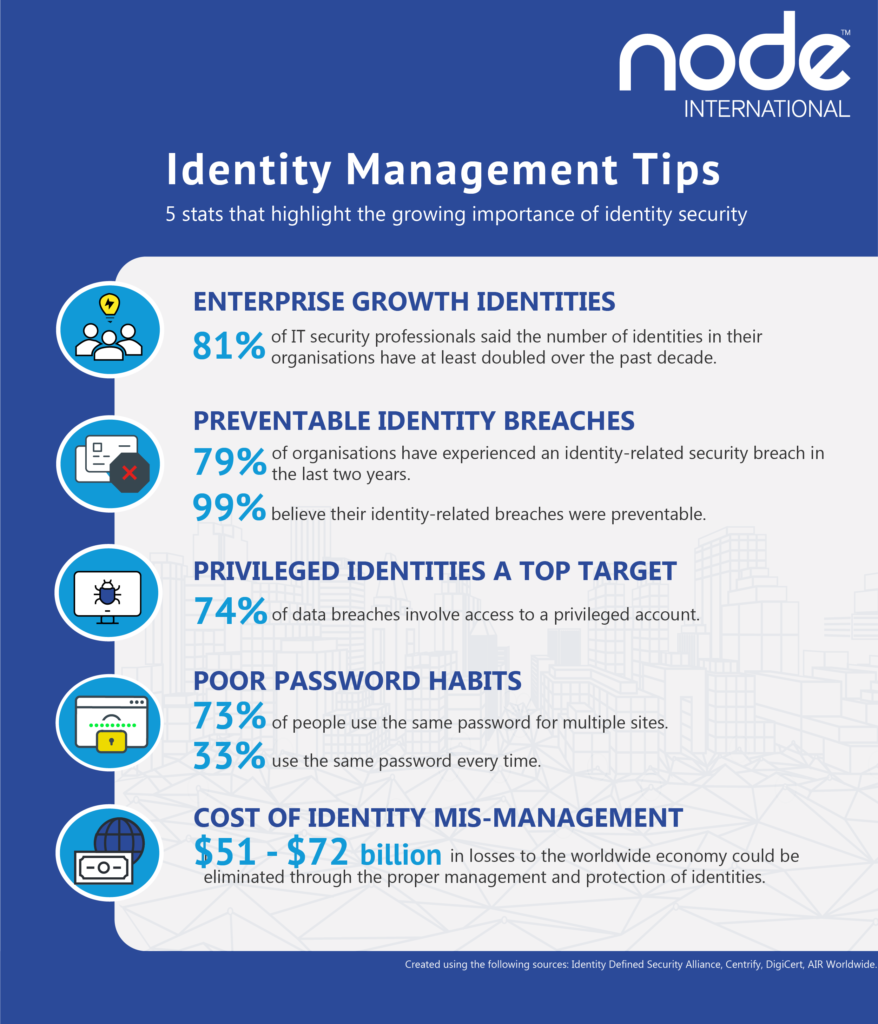
Identity management is focused on protecting the identities of employees and clients. Compromised employees’ identities can be used by hackers to gain access and wreak havoc on unexpecting companies.
Cybersecurity insurance can help protect businesses from the negative impact of exposed identities.
One way we may protect our insured’s clients from identity theft after a data breach is by activating credit monitoring. If criminals try to use their leaked data to commit financial fraud this will be flagged and prevented.
5 stats that highlight the growing importance of identity security.
An advanced Microsoft Office 365 phishing campaign is being launched at C-level executives, executive assistants, and financial departments.
Some of these attacks see newly-appointed, unannounced CEO’s as victims. In these cases, attackers try to take advantage of the executives during their transition period to gain unauthorized access to the account.
Attackers try to compromise any company account or a 3rd party partner and then use collected sensitive information to create more sophisticated attacks to phish C-level executives.
This campaign began in early December 2020 and is still ongoing as of March 2021. The attackers are leveraging phishing toolkits and many sophisticated methods.
Most of the phishing emails are sent from addresses with Microsoft-themed sender domains, with properly configured SPF records and are made to look like messages from the company, carrying fake alerts about “Important Service Changes”, “Important Security Policy Update”, etc.
The majority of the targeted email accounts used the format first name.last name@company domain, making full names in the attachments easy to automate. But even in cases where only initials appeared in the email address, the attackers still included the victim’s full name in the PDF attachment. This suggests the threat actors conducted additional prior research to carefully carry out spear phishing attacks.
Through malicious attachments, the victim is sent to a spoofed Microsoft-looking themed webpage with a fake Office 365 login page. If the victim enters their account credentials into the phishing portal, the attacker can then verify it was a valid Office 365 address. If after the victim enters their credentials, the victim may simply be redirected to the legitimate sign-in website like nothing ever happened.
How to Protect Yourself
Sophisticated phishing attacks are hard to detect with typical tools and methods because they do not use malware or malicious URLs that can be detected by antivirus. While it is important that you always use updated end-point protection and antivirus, mitigating this threat is hard. Here are some best practices:
- End-user training, awareness, and education is critical so end-users know to verify a request as legitimate and stay alert for unexpected emails with links or attachments. For example, employees should be on the alert for poor spelling and grammar and spoofed app names, domain URLs and email addresses.
- Implement two-factor authentication (2FA) for email. This is one of the best defences against phishing, because even if the attacker steals a user’s credentials, they won’t be able to gain access without the second factor.
- Configure your email to filter out suspicious looking phishing emails. Depending on your email filter, this may be turned on by default.
- Prohibit employees from being able to navigate to sites not whitelisted via a web filter. If you have a web filter, have your network administrator or authorized IT professional configure it to prohibit users from accessing unsafe and spoofed websites.
Node Prevent
When you purchase one of our cyber insurance policies we include Node Prevent, a free service with employee training, how to implement best practices and threat alerts such as these.
About Node International
We provide leading comprehensive insurance coverage combined with essential cybersecurity prevention and detection tools.
Important Recommendation
Menu
Legal
Our Office :
One Minster Court
Mincing Lane
London
EC3R 7AA
Interested in Cyber Insurance?
[mc4wp_form id=”5523″]



Recent Comments